Supply Chain Risk Management (SCRM) for AI Infrastructure
Securing GPU-Based Systems from Procurement to Deployment
Why Supply Chain Integrity Is Now Mission-Critical
As federal agencies accelerate adoption of AI, high-performance computing, and GPU-based infrastructure, the focus on security is shifting upstream. It is no longer sufficient to secure systems after deployment-the integrity of infrastructure must be assured from the moment it enters the supply chain through secure sourcing and end-to-end traceability.
Supply Chain Risk Management (SCRM) addresses this challenge by embedding security, validation, and traceability across the entire lifecycle of IT systems. Guidance from the National Institute of Standards and Technology (NIST), particularly SP 800-161, reinforces that supply chain security is not optional-it is foundational to mission assurance.
In AI-driven environments, supply chain risk is operational risk.
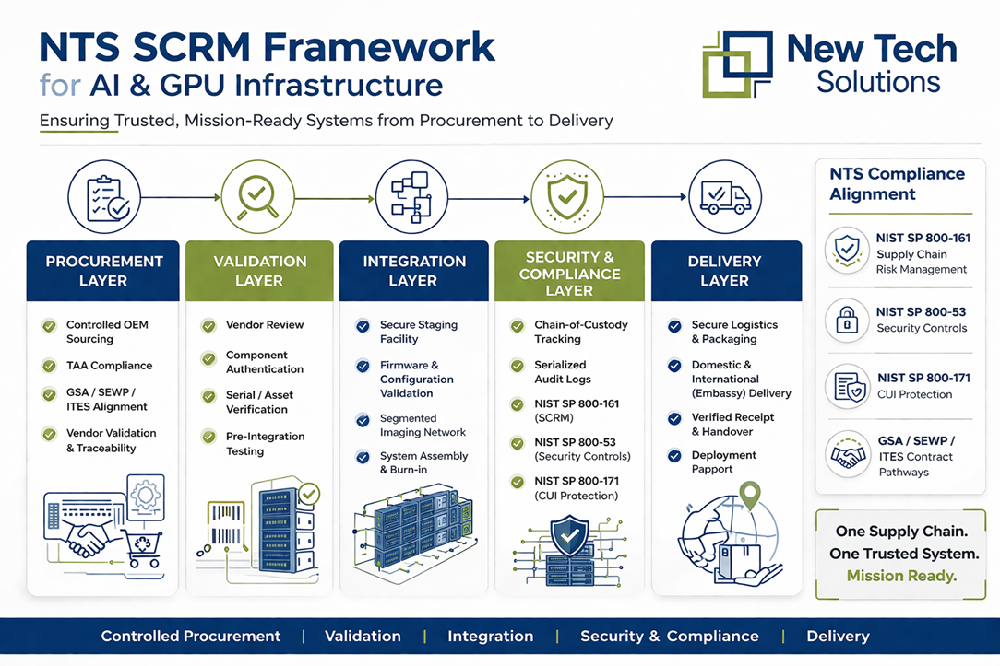
NTS Secure Supply Chain Framework for AI & GPU Infrastructure
Defining Supply Chain Risk Management in Federal IT Environments
Supply Chain Risk Management (SCRM) is the structured discipline of identifying, assessing, and mitigating risks across the full lifecycle of technology systems-from procurement and sourcing through validation, integration, and final delivery. In federal IT environments, where mission assurance and security are paramount, SCRM ensures that every system is authentic, untampered, and secured at both the hardware and firmware levels.
Beyond basic verification, SCRM provides end-to-end traceability across the supply chain, enabling organizations to maintain visibility and control over every component and process involved in system delivery. This approach aligns infrastructure with established federal security frameworks and ensures that systems are not only compliant but also trusted and operationally reliable from the moment they are deployed.
THE NEW RISK LANDSCAPE (AI + GPU INFRASTRUCTURE)
AI infrastructure introduces a new level of complexity and exposure that fundamentally changes the supply chain risk landscape. These environments rely on high-value GPU components sourced through global supply chains and require tightly coupled integration across compute, networking, and storage layers. This multi-dimensional architecture expands the attack surface, particularly at the hardware and firmware levels, while also increasing the risk of product substitution or tampering during transit.
Unlike traditional IT deployments, AI environments are built on fully integrated platforms rather than standalone components. As a result, supply chain integrity must extend beyond individual parts to encompass the entire system, making end-to-end validation and control essential to ensuring trusted, mission-ready infrastructure.
NTS 5-LAYER SCRM FRAMEWORK
Procurement Layer - Secure Sourcing
NTS ensures that all components are sourced exclusively through authorized OEM channels, maintaining strict alignment with Trade Agreements Act (TAA) requirements and established federal procurement pathways, including GSA, SEWP, CIO-CS, and ITES. This controlled sourcing approach provides full traceability and reduces exposure to counterfeit or unauthorized products, ensuring that only trusted, verified components enter the supply chain.
Validation Layer - Component Verification
Each component undergoes rigorous validation prior to integration, including firmware verification, configuration checks, and authenticity confirmation. This process ensures that all hardware meets established security and performance baselines, preventing compromised or non-compliant components from entering the system environment.
Integration Layer - Secure System Assembly
Systems are assembled within controlled staging and integration environments designed to maintain strict security and operational integrity. NTS utilizes segmented networks, secure imaging processes, and standardized configuration baselines to build and validate systems prior to deployment. These activities are performed within enterprise-grade facilities aligned with industry quality and process standards, ensuring consistency, repeatability, and audit readiness across all deployments.
Security & Compliance Layer - Framework Alignment
All systems are aligned with established federal security and supply chain risk management frameworks, including NIST SP 800-161 for supply chain risk, NIST SP 800-53 for security controls, and NIST SP 800-171 for the protection of Controlled Unclassified Information (CUI). NTS integrates these requirements throughout the lifecycle, ensuring that systems are designed, configured, and validated in accordance with federal standards.
This alignment enables consistent application of security controls, supports audit readiness, and ensures that infrastructure can be deployed within regulated environments without additional remediation. By embedding compliance into the build and integration process, NTS ensures that systems are not only operationally ready but also meet the security expectations required for mission-critical federal deployments.
Delivery Layer - Chain-of-Custody Assurance
NTS ensures that all systems are delivered through controlled logistics processes that maintain full chain-of-custody from integration to final destination. Each asset is tracked using serialized identification and documented handling procedures, providing complete visibility and accountability throughout transit. This approach minimizes the risk of loss, substitution, or unauthorized access while ensuring that all systems remain intact and verifiable upon arrival.
Delivery processes are further supported by secure shipping protocols and validation procedures tailored to federal requirements, including support for both domestic and international deployments. Upon receipt, systems can be verified against expected
configurations and asset records, ensuring that infrastructure arrives exactly as intended-secure, uncompromised, and ready for immediate deployment.
Most organizations operate within fragmented delivery models, where procurement and system integration are handled separately - introducing gaps in accountability, visibility, and control across the supply chain. Resellers typically focus on sourcing, while integrators focus on deployment, leaving critical validation and traceability steps disconnected.
NTS eliminates this fragmentation by combining procurement authority with deep integration expertise, creating full lifecycle control from sourcing through delivery. This unified approach enables complete Bill of Materials (BOM) validation, secure pre-integration of GPU and AI systems, and rack-level delivery with full system verification. The result is reduced deployment risk, accelerated time to mission, and infrastructure that arrives fully validated and ready for immediate operational use.
WHY IT MATTERS FOR FEDERAL & FSIs
For federal agencies and system integrators, Supply Chain Risk Management (SCRM) has evolved into a strategic requirement that directly influences mission success. As infrastructure becomes more complex-particularly with the adoption of AI and GPU-based systems-risks introduced at the supply chain level can impact systems before they are even operational. Without embedded SCRM, organizations are forced into reactive validation, where issues are identified late in the deployment cycle, increasing operational risk, delaying timelines, and introducing uncertainty into mission-critical environments.
NTS addresses this challenge by integrating SCRM as a core operational capability rather than a downstream compliance activity. Through end-to-end control across procurement, validation, integration, and delivery, NTS ensures that systems arrive secure, fully validated, and ready for immediate deployment. This proactive approach mitigates risk before it enters the environment, embeds compliance directly into the delivery process through strong framework alignment, and enables agencies and integrators to deploy infrastructure with confidence, speed, and full accountability.
As AI adoption continues to accelerate, the integrity of infrastructure can no longer be assumed-it must be engineered, validated, and delivered with precision. NTS ensures that every system is trusted from the start, providing a foundation for secure, mission-ready operations across AI infrastructure and high-performance computing. One Supply Chain. One Trusted System. Mission Ready.